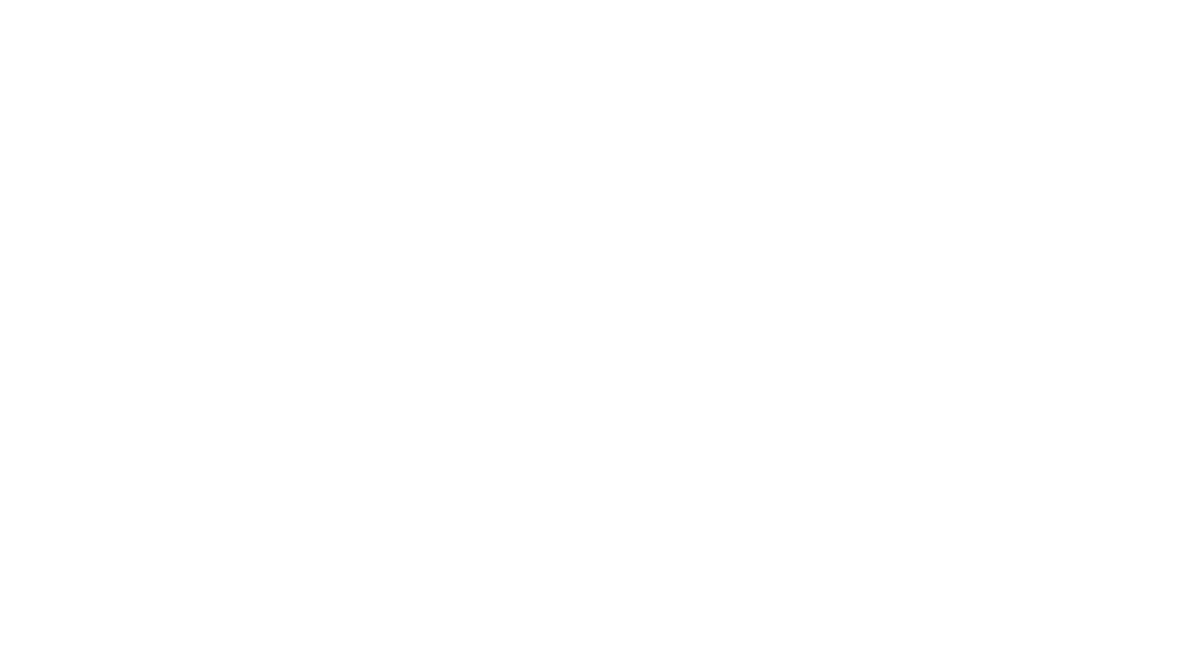
The numbers are staggering and frankly, a little terrifying. Ransomware attacks have exploded by 146% in recent months, while data exfiltration has surged by 92%. But here's what's really keeping cybersecurity experts up at night: these aren't your garden-variety ransomware attacks anymore.
We're dealing with AI-powered threats that can think, adapt, and evolve faster than most businesses can respond. These smart attacks are operating autonomously, learning from each encounter, and getting better at bypassing traditional security measures every single day.
If you think your current security setup is enough, you might be in for a rude awakening. Let's dive into the seven critical mistakes most businesses are making right now—and more importantly, how to fix them before it's too late.
The New Reality: AI-Powered Ransomware is Here
Before we jump into the mistakes, you need to understand what we're up against. The ransomware landscape has completely transformed. We're seeing 34 new ransomware families emerge as cybercriminals get more creative and aggressive. Groups like Qilin have doubled their activity, while others like Hunters International have abandoned traditional file encryption entirely in favor of stealthier data-only extortion.
The game-changer? AI-powered malware that can operate without human supervision, learning to dodge detection systems in real-time and spreading across networks in minutes, not hours.

Mistake #1: Underestimating AI-Enhanced Social Engineering
The Problem: Most businesses still treat phishing like it's 2019. Your employees are trained to spot obvious fake emails with poor grammar and suspicious links, but AI has completely changed the game.
Modern ransomware groups are using AI to create personalized, convincing communications that can fool even security-aware employees. These aren't mass-produced spam emails anymore—they're carefully crafted messages that reference real company information, use proper grammar, and sound exactly like they came from a trusted colleague or vendor.
The Fix: Your employee training needs a serious upgrade. Start conducting regular phishing simulations using AI-generated content that mimics the latest attack patterns. Teach your team to verify any unusual requests through a secondary communication channel—even if the email looks perfect.
Create a culture where questioning suspicious communications is rewarded, not discouraged. And implement multi-factor authentication everywhere, because even if someone falls for a sophisticated phishing attack, you'll still have an extra layer of protection.
Mistake #2: Relying on Outdated Detection Methods
The Problem: If you're still depending on traditional antivirus software and signature-based detection systems, you're fighting tomorrow's war with yesterday's weapons.
AI-driven ransomware like BlackMatter uses intelligent encryption strategies and analyzes your defenses in real-time to find ways around them. These threats adapt faster than traditional security tools can keep up with.
The Fix: Upgrade to AI-powered endpoint detection and response (EDR) systems that can identify behavioral anomalies rather than just known threat signatures. These systems learn what normal network activity looks like and flag anything unusual.
Consider implementing zero-trust architecture where every access request is verified, regardless of where it comes from. This approach assumes that threats could already be inside your network and verifies everything accordingly.

Mistake #3: Focusing Only on Encryption Prevention
The Problem: Many businesses are still preparing for ransomware attacks from five years ago. They focus on backup and recovery strategies to deal with encrypted files, but they're missing the bigger threat.
Today's attackers have shifted to an "exfiltration-first" strategy. They steal your sensitive data first, then threaten to release it publicly if you don't pay up. Even if you have perfect backups, you still face the nightmare of having your customers' personal information, trade secrets, or financial data leaked online.
The Fix: Implement comprehensive data loss prevention (DLP) strategies. This means knowing exactly what sensitive data you have, where it's stored, and who has access to it.
Use data classification tools to identify and tag your most critical information. Monitor data access patterns and set up alerts for unusual activity, like someone downloading large amounts of sensitive files or accessing data they don't normally need.
Encrypt sensitive data both at rest and in transit, and consider using data masking techniques for non-production environments.
Mistake #4: Inadequate Protection for High-Value Assets
The Problem: AI-powered malware has gotten smart about targeting what matters most. Instead of randomly encrypting files, these systems specifically hunt for databases containing financial records, customer information, intellectual property, and other high-value assets.
Many businesses treat all their data equally from a security perspective, which means their crown jewels often don't get the extra protection they deserve.
The Fix: Conduct a thorough data inventory to identify your most critical assets. This includes customer databases, financial records, proprietary research, and any information that would be devastating if leaked or destroyed.
Implement additional security layers for these high-value assets, including enhanced monitoring, stricter access controls, and separate backup systems. Consider using network segmentation to isolate critical systems from the rest of your network.
Regular penetration testing should specifically focus on how well you're protecting these assets, not just general network security.

Mistake #5: Neglecting Healthcare and Industry-Specific Vulnerabilities
The Problem: Certain industries are getting hammered harder than others. Healthcare facilities are facing relentless attacks, with groups like INC Ransom accounting for nearly 17% of attacks on hospitals and clinics.
But it's not just healthcare. Any business that has recently automated critical systems—including manufacturing, logistics, and infrastructure companies—is facing increased risk because these newly connected systems often lack proper security controls.
The Fix: If you're in a high-risk industry, you need industry-specific security measures. For healthcare organizations, this means ensuring all medical devices are properly secured and regularly updated.
For businesses with newly automated systems, conduct security assessments of all connected devices and implement proper network segmentation to prevent lateral movement if one system gets compromised.
Consider working with security providers who specialize in your industry and understand the unique threats you face.
Mistake #6: Ignoring Supply Chain Vulnerabilities
The Problem: You might have bulletproof security, but what about your vendors? Supply chain attacks are becoming increasingly common because it's often easier for attackers to compromise a trusted third party than to attack you directly.
Many businesses focus on securing their own systems while giving trusted vendors and partners broad access without proper oversight.
The Fix: Implement a comprehensive vendor risk management program. This means security assessments for all third-party providers who have access to your systems or data.
Require vendors to meet specific security standards and provide regular attestations of their security practices. Use least-privilege access principles for vendor accounts, giving them only the minimum access needed to do their job.
Monitor vendor access carefully and have incident response procedures that account for potential vendor compromises.
Mistake #7: Reactive Instead of Proactive Security Posture
The Problem: Most businesses wait until after an attack to address their security gaps. This reactive approach leaves you vulnerable during the critical window when AI-powered attacks can spread rapidly across your entire network.
By the time you detect most ransomware attacks, it's already too late—the damage is done, and you're in crisis management mode.
The Fix: Shift to a proactive security model with continuous monitoring and threat hunting. This means actively looking for signs of compromise rather than waiting for alerts.
Implement 24/7 security operations center (SOC) monitoring, either in-house or through a managed security service provider. Regular vulnerability assessments and penetration testing should be standard practice, not something you do once a year.
Develop and regularly test incident response plans that specifically address AI-powered ransomware scenarios. Your team needs to know exactly what to do in the first few minutes of an attack, because that's when response speed matters most.

The Bottom Line: Act Now, Before It's Too Late
The 146% surge in AI-powered ransomware attacks isn't just a statistic—it's a wake-up call. These sophisticated threats are evolving faster than most businesses can adapt, and the stakes have never been higher.
The good news? You don't have to face these threats alone. With the right strategy, tools, and expert guidance, you can build defenses that are every bit as intelligent as the attacks trying to penetrate them.
Don't wait until you become another ransomware statistic. The cost of prevention is always less than the cost of recovery—and with AI-powered attacks, recovery might not even be possible.
Ready to protect your business from AI-powered ransomware attacks? Contact B&R Computers today for a comprehensive security assessment. Our team of cybersecurity experts will help you identify vulnerabilities, implement advanced defenses, and build a security strategy that can stand up to even the most sophisticated AI-powered threats. Learn more about our proactive IT management approach and discover how we're helping businesses stay one step ahead of cybercriminals.