The Cyber Supply Chain: Today’s Ultimate Attack Vector
Think your business is protected because your firewalls are tight and your employees are trained? Think again. Supply chain attacks have become a hacker favorite—one weak point in your vendor ecosystem, and everyone is at risk.
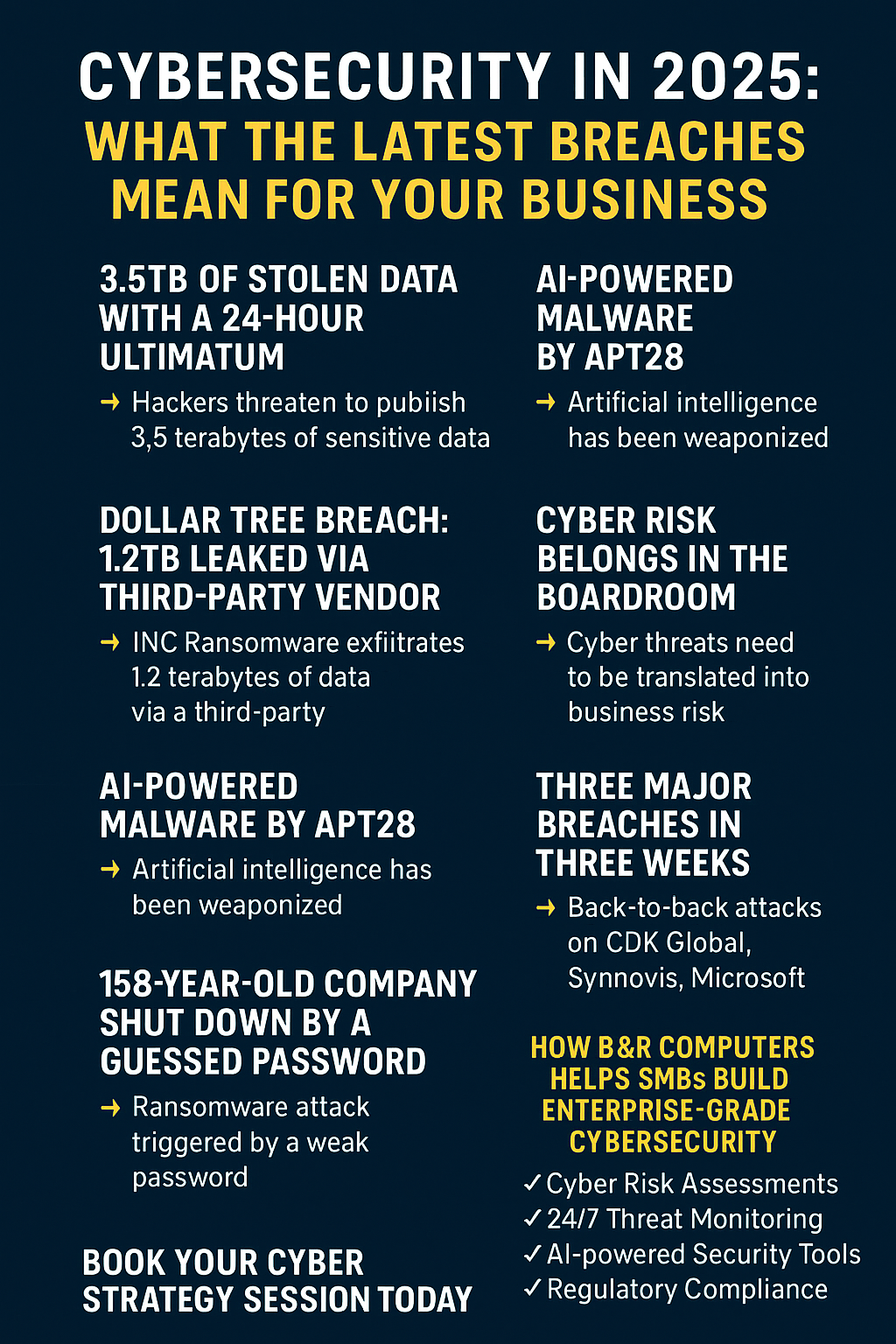
This isn’t just theory. According to recent findings, a whopping 62% of breaches now originate with third-party vulnerabilities. The manufacturing sector alone reported 22% of all cyberattacks with a known industry victim, marking its third straight year as the #1 target. And no industry is immune—from healthcare to professional services, every business connected to another is exposed.

Why Are Supply Chain Attacks Booming?
1. Maximum Impact, Minimal Effort
Cybercriminals go after vendors because it’s the most efficient way in. A single compromised supplier can open doors to dozens (or hundreds) of their customers, multiplying the potential payoff.
2. Exploiting Trust
Organizations trust their vendors, systems, and platforms. Hackers use that trust to slip in undetected, leveraging legitimate software updates, service relationships, or APIs to gain access.
3. Ripe Targets
Many small and mid-sized vendors don’t have the IT defenses of the Fortune 500. Attackers have taken notice. If your partner’s security isn’t tight, your data (and money) could be the next prize.
Real-World Case Studies: The High Cost of Compromised Links
The SolarWinds Shockwave
This was the breach that changed everything. In 2020-2021, hackers inserted malicious code into SolarWinds’ Orion software. When customers—including government agencies and Fortune 500 firms—applied a routine update, the hackers got instant access to thousands of networks. The damage? Still being fully calculated, but the lesson is clear: third-party software can be a Trojan horse.
Manufacturing Mayhem
During the COVID-19 pandemic, supply chain targets showed their fragility. Massive cyberattacks on meatpacking and semiconductor factories led to weeks-long shutdowns. Even brief interruptions cost Fortune 500 companies up to 11% of annual revenues, with global losses running into the trillions. These weren't just business hiccups, but events that threatened entire national economies.
The CrowdStrike Outage Lesson
While not a cyberattack, the 2024 CrowdStrike outage proved how one provider’s hiccup can disrupt the world. Global internet slowdowns, airline delays, and financial losses served as a real-time lesson: it doesn’t take a breach—just a single tech supplier problem—to upend business.

Where Are the Vulnerabilities?
Open Source Dependencies: Modern apps often rely on dozens (or hundreds) of open-source libraries. Attackers slip malicious code into legitimate projects, knowing it might flow downstream into thousands of businesses.
Commercial Software Weaknesses: Many mainstream software tools contain hidden flaws or outdated code. Cybercriminals (and nation-state attackers) are getting better at finding and exploiting these.
Operational Technology (OT): Manufacturers often run critical systems that weren’t designed for networked environments. Once those environments connect to IT networks or vendors, attackers step right through.
Build Pipelines & Development Tools: Hackers are increasingly focused on the very tools used to build software—injecting malicious elements during the development process. Once released, compromised tools spread malware far and wide.
New Frontiers: AI, Crypto & More
A new wave of attacks in 2024 and 2025 targeted:
- AI/ML infrastructure, using AI-generated code or vulnerabilities in machine learning tools as backdoors.
- Cryptocurrency providers, where attackers have stolen millions by exploiting vendor weak spots and diverting funds from digital wallets.
- Critical infrastructure, blending old-school phishing with advanced persistence to deliver ransomware or steal sensitive data.
The lesson? If it connects to your business, it can become an attack vector.
What Smart Businesses Are Doing Differently
Map Your Dependencies
Most companies don’t know their full vendor landscape—or how those relationships interlock. Start mapping your digital supply chain. Who supplies your tech, software, IT, data processing, and cloud services? If a third-party vendor vanished tomorrow, what would break?
Implement Zero Trust
Zero trust architecture is essential. Stop assuming anyone—or any application—should have automatic network access. Every login, system, and access point must be verified, monitored, and locked down as if it’s already suspect.
Screen & Monitor Vendors Like a Hawk
A simple yes/no security questionnaire isn’t enough. Require up-to-date certifications, request proof of regular security testing, and institute continuous monitoring of your vendors’ risk status. Automate alerts for new vulnerabilities or incidents in your supply chain.
Test Incident Response for Supply Chain Attacks
Ransomware plans aren’t enough—your incident response plan should specifically address supply chain breaches. Who do you call if a major vendor is compromised? How quickly can you isolate or uninstall their software?
Make Cybersecurity a Boardroom Issue
Cyber risk isn’t just a tech problem; it’s a business risk. Regularly brief leadership teams on supply chain risk exposures, recovery plans, and ongoing vendor assessments. Clear communication means faster, more effective action when (not if) things go sideways.

Don’t Wait: How B&R Computers Can Help
No business exists in a vacuum anymore—your digital ecosystem stretches across dozens of partners, providers, and platforms. A vulnerability anywhere could affect you everywhere.
Here’s how we can help at B&R Computers:
- Run a comprehensive audit of your current vendor landscape and digital dependencies
- Help you set up a zero trust architecture, tailored for your industry
- Recommend automated tools for real-time vendor monitoring and threat detection
- Test and revise your incident response plan specifically for supply chain scenarios
- Deliver ongoing cybersecurity awareness training so your team is ready for anything
Want to make your business a hard target in today’s threat landscape? Contact our team today for a personalized supply chain risk assessment and peace of mind.
Learn more practical tips in our Cyber Hygiene Checklists or dive deeper into real-world breach stories from our clients in this blog post.
Stay ahead. Stay secure. The weakest link in your supply chain doesn’t have to be yours.