Cyber insurance was once seen as a handy last line of defense if your business fell victim to a data breach or ransomware. In 2025, it’s become a requirement—but also one of the most confusing and, let’s be honest, frustrating parts of your cybersecurity strategy. Premiums rise, policies get more complicated, and coverage exclusions lurk in the fine print. At B&R Computers, nearly every client asks us: “Do I really have the coverage I think I do?”
Let’s dig in and make sure you’re not just paying for a false sense of security.
The New Era: Why Insurers Are Tightening the Screws
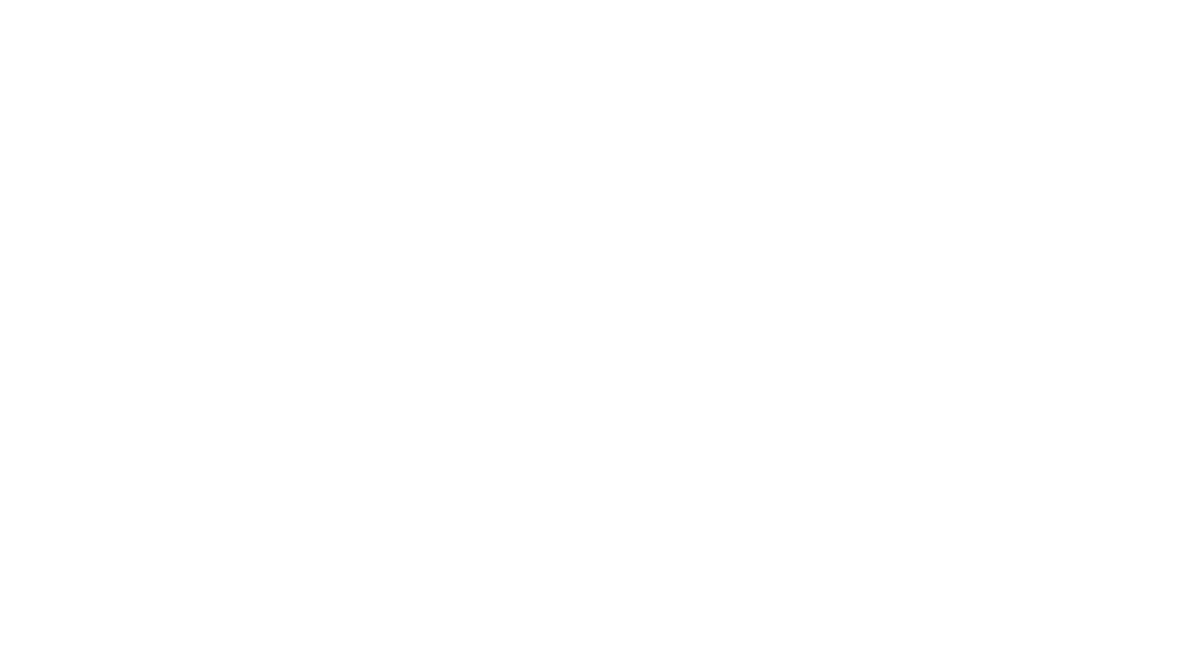
Cybercrime has absolutely exploded. Global damages are expected to hit $10.5 trillion this year—a number almost impossible to wrap your brain around. With claims skyrocketing (over 33,000 filed last year in the U.S. alone), insurers are getting brutal about which businesses they’ll actually cover and when they’ll pay out.
What’s changed?
- Stricter requirements: You can’t buy a policy without proof of mature cybersecurity controls. MFA, regular security awareness training, up-to-date backups, and incident response plans are now table stakes.
- Heavier scrutiny on small business: Cybercriminals know small and midsized businesses are softer targets. If you don’t look serious about security, you’re either denied or shoved into the “sky-high premium” bin.
- Coverage no longer “one size fits all”: Carriers are asking tough questions about your IT stack, network security, and even your vendor relationships.

What Your Policy Doesn’t Cover (But You Thought It Did)
Pre-Existing Vulnerabilities
If you have old systems, unpatched software, or risky network setups—and you knew about them—don’t expect a payday from your insurer if hackers break in. Most policies specifically exclude payouts for events tied to “known but unremediated” security holes. Review your last vulnerability scan: are any doors still open?
Unencrypted Devices
Lost laptop? Stolen phone with sensitive emails? If devices aren’t properly encrypted, many policies flatly refuse to cover any breach-related costs. Encryption is no longer optional—it’s the difference between a payout and a denial letter.
Social Engineering Attacks
Classic phishing and CEO fraud have caused more financial damage to B&R Computers clients than “traditional” hacking. But here’s the trap: without a specific social engineering endorsement, your claim for losses from cleverly worded phishing emails will get tossed out. Review your declarations page—does it actually mention “social engineering” or “fraudulent instruction” coverage?
Insider Threats
An employee or partner deliberately leaking data—or acting negligently—often isn’t covered. Standard policies typically only apply to “external” threats unless you negotiate for an extension to include insider misconduct.
War & Terrorism Exclusions
With international cyberattacks on the rise, insurers have instituted sweeping “war” exclusions. Translation: if your systems go down in a geopolitical cyber skirmish, even if you’re collateral damage, your policy will probably exclude it. Always ask your carrier: “How does this policy define (and limit) cyber ‘war’ or nation-state events?”

Policy Period Pitfalls: Timing Is EVERYTHING
Here’s a scenario we see all the time at B&R Computers: a breach begins months before it’s detected. You switch insurers midyear, only to discover the attack started on the old policy’s watch, but you report it under the new one. The result? Both carriers deny the claim—one says it happened after their coverage ended, the other says it started before they began.
The fix: Ask about “tail coverage” or “extended reporting period” options when changing providers. Never let time gaps sneak in between policies.
Did You Close the “Protection Gap”?
Despite record insurance demand, there’s a massive “protection gap” in the real world. Only a fraction of businesses have the coverage they really need—not just a policy, but one that:
- Matches your industry’s unique risks
- Reflects your actual IT and physical security measures
- Covers modern exploits, not just last decade’s threats
Many small and midsized businesses are underinsured or left exposed to exclusions they don’t understand until it’s too late.

Five Things Every CEO Should Do to Avoid Insurance Regret
Want to avoid the gut-punch of a denied claim? Here’s what we advise all our clients:
-
Get a Security Health Check—Yesterday
Run frequent vulnerability scans and patch everything, everywhere. Schedule regular external audits. Demonstrate you’re proactive—not reactive. -
Know Your Exclusions
Insist your broker explain the fine print. If a policy clause sounds vague (“unauthorized access by employees”), drill down until you understand exactly what’s not covered. -
Buy the Right Endorsements
If your operations involve wire transfers, cloud-based data, or heavy vendor interaction, make sure your policy has endorsements for:- Social engineering fraud
- Vendor/third-party breaches
- Hardware replacement (not just data recovery)
- Ransomware response
-
Align Policy Reporting With Your IR Plan
Policies require incidents be discovered and reported within certain windows. Map your incident response plan so you can notify your carrier immediately—delay = denial. -
Review Annually & Whenever Your Operations Change
New tech? Different vendors? A major staff or workflow change? Time for a policy review.

Why DIY Doesn’t Cut It Anymore
In 2025, nearly every successful claim we see stems from a business that was proactive—about both cybersecurity and keeping their policy current. Unfortunately, most denials happen because of overlooked details or a false sense of “set and forget” coverage.
With cyber insurance evolving so quickly, it pays to have a seasoned IT partner at your side—not just for managing endpoints and servers, but for decoding policy jargon and helping you check every box the insurer requires.
Ready for a Real Safety Net?
Don’t wait for a claim denial—or worse, a paralyzing attack—to discover your policy’s limits.
Connect with B&R Computers for a no-nonsense cyber insurance readiness review. We’ll walk you through your coverage, point out gaps, and show you how to build the cyber resilience that both your insurer and your business demand.
Start your cyber risk checkup with us today.
Want more practical tips? Check out our recent guides:
- Cyber Hygiene Checklists: Simple Steps for Businesses to Stay Secure in 2025
- The Most Overlooked Cyber Risks for Real Estate, Insurance, and Finance Professionals
- Why Regular Cybersecurity Training is Your Secret Weapon Against Breaches
Stay safe—and make sure your insurance actually has your back!