Collaboration apps like Zoom, Microsoft Teams, Slack, and others have reshaped how businesses connect, share, and operate—especially for fast-paced sectors like accounting, insurance, and real estate. But as these tools become more essential, they’re also becoming prime targets for cybercriminals looking for new ways to break in.
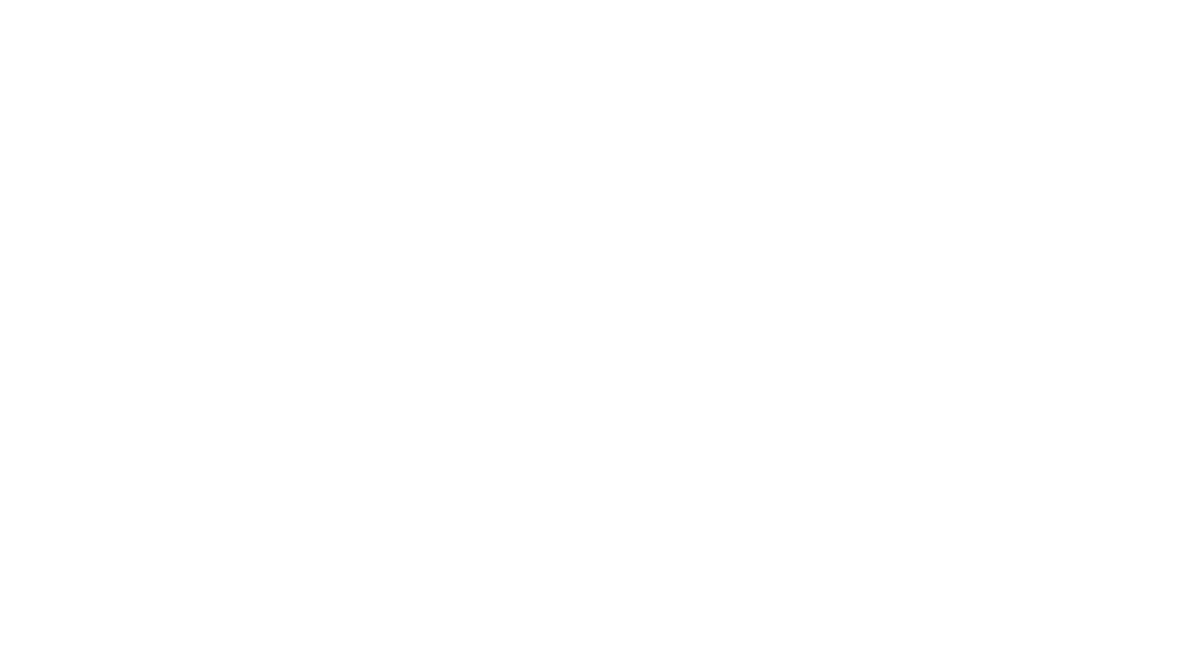
In 2025 alone, there’ve been headline-grabbing vulnerabilities and new strategies that hackers are using to attack businesses simply by exploiting the tools you trust the most. If you think your business is too small to make the list, think again—these threats don’t discriminate by company size.
Let’s dive into how these everyday tools are making businesses vulnerable, recent case studies, and most importantly, what you can do to protect your company and clients.
The New Weak Link: Collaboration Platforms in the Crosshairs
Just a few years ago, the biggest cyber threats targeted email. Today, collaboration platforms are the new entry point.
Why? Because your employees spend hours a day on these tools, and trust their notifications, contacts, and even unexpected meeting invites. Hackers know this, and they’re always scanning for the latest way in.
Why Zoom and Teams?
- Ubiquity: Almost every modern business uses one (or both).
- Trust: It’s normal to receive unexpected invites, messages, or file shares.
- Feature Creep: Frequent feature additions can create unknown vulnerabilities.
- Cross-device access: Employees connect from phones, laptops, home devices, and more.
Real-World Vulnerabilities in 2025: A Look at Zoom (and Beyond)
Let’s start with Zoom, which—despite security updates—remains in hackers’ crosshairs. Here’s what we’ve seen this year:
1. Time-of-Check Time-of-Use (TOCTOU) Vulnerability
- CVE-2025-30663
May 2025 saw a high-severity TOCTOU vulnerability that allowed attackers to manipulate resources in the split-second between verification and execution. If exploited, this can let hackers escalate privileges or even run arbitrary code on a user’s device. - Bottom line: If you didn’t patch immediately, your business may have been exposed.
2. NULL Pointer Dereference Vulnerabilities
- CVE-2025-30665, CVE-2025-30666, CVE-2025-30667, CVE-2025-30668
These bugs could cause Zoom Workplace Apps to crash or, worse, lead to attackers executing their own code.
3. Buffer Over-read (Windows Users Beware)
- CVE-2025-46785
A flaw in Zoom’s Windows workplace client allowed attackers to access portions of memory that should’ve been private—risking exposure of sensitive business data.
4. Past Issues That Still Linger
Remember Zoom’s old bug? Windows users who clicked certain file links would unknowingly hand over login credentials to attackers who crafted malicious invitations. This classic “feature turned flaw” proves how collaboration can become exposure.
Most importantly: these bugs didn’t just affect Zoom, but versions on Windows, macOS, Linux, iOS, and Android. No device was immune.
Attack Tactics: How Hackers Trick and Exploit
Knowing the vulnerabilities is just step one. Here’s how hackers actually use them:
Social Engineering Inside Trusted Spaces
Think you’re savvy enough not to fall for phishing? Hackers use official-looking Zoom or Teams notifications, meeting requests, and file shares. Because these requests come through platforms staff use daily, they’re more likely to get clicks.
- “You’ve been added to a meeting—click to join!”
- “Your manager shared a file with you.”
With the right vulnerability, one click can grant an attacker access to your whole business network.
Credential Theft
Some flaws (like Zoom’s old UNC link bug) let hackers silently steal login credentials when a user simply clicks a malicious link inside a chat or meeting room—no malware required.
Cross-Platform Exploitation
Modern attacks don’t stop with Windows. Vulnerabilities are leveraged across operating systems, including macOS and mobile devices. For example, Mac users faced risks via modules handling camera or microphone—hackers could create persistent access to sensitive audio or video feeds.
Lateral Movement Across Cloud and Local Resources
Once inside, attackers can use your collaboration tools to move across systems—accessing files on SharePoint, Google Drive, or your local network, depending on what’s connected to your Teams or Zoom instance.
What Does This Mean for Financial, Real Estate, and Insurance Firms?
Let’s face it: a compromised Zoom or Teams account can be a goldmine for criminals—especially if your work involves personal client data, financial documents, or insurance records.
- CPA & Tax Professionals: Sensitive financial data and Social Security numbers are accessed and shared daily via these platforms.
- Real Estate & Property Management: Leases, personal identity docs, wire transfer instructions—all at risk.
- Insurance: Policyholder data and claims communications are juicy targets for fraudsters.
A vulnerability in one user’s account could lead to compromised client records, wire fraud, data breaches that must be reported, or even regulatory action.
How Businesses Should Respond: Prevention is the New Cure
Staying ahead isn’t just about the latest patch—it’s about rethinking everyday habits. Here’s how to start:
1. Patch Early, Patch Often
Zoom, Teams, Slack, and other vendors rush patches as soon as vulnerabilities are found. Set up automatic updates wherever possible, and train staff to always update software before using it for critical work. 
2. Enable Multi-Factor Authentication (MFA)
No password (no matter how complex) is enough. Requiring MFA on collaboration tools makes it exponentially harder for attackers to take over accounts—even if they do steal login credentials.
3. Train Your Team—Continuously
Technical defenses are essential, but nothing beats awareness. Schedule quarterly cybersecurity training focused on:
- Spotting fake invites and links
- Verifying meetings and files, especially if they’re unexpected
- How to report suspicious activity quickly
4. Control Access and Permissions
Don’t give every employee admin or full file access “just in case.” Use role-based controls, and regularly audit which users can access sensitive channels, files, or data stores linked to collaboration tools.
5. Monitor for Unusual Activity
Look for signs someone is already inside: logins from strange locations, new meeting invitations, or unknown files shared suddenly. If you don’t have tools for this, now’s the time to consider a managed cybersecurity provider (like us at B&R Computers).
6. Plan for Recovery
Assume breaches will happen. Have a plan for how you’ll respond—who to notify, how to reset compromised accounts, and how to keep the business running while the problem is fixed.
Don’t Let Fast-Moving Hackers Outpace Your Business
The convenience of Zoom, Teams, and other collaboration platforms is undeniable. But as cyber threats evolve, so should your defense strategy.
If your business can’t afford a day of downtime or the risk of client data loss (and who can?), proactive security is a necessity—not a luxury. At B&R Computers, we specialize in helping financial, real estate, and insurance businesses stay one step ahead with tailored cybersecurity strategies that match the way you actually work—no oversized, overpriced solutions required.

Our proactive, adaptive approach means we patch fast, monitor continuously, and train your staff to outsmart even today’s most advanced tricks. It’s no wonder we’re five-star rated on Google and trusted by business owners across the region.
Ready to Secure Your Most Important Assets?
Don’t wait for an incident to highlight the weaknesses in your daily tools. Let’s work together to safeguard your business, reputation, and clients—starting today.
Visit B&R Computers or contact our team for a free cybersecurity assessment tailored to your needs.